For decades, video games have been dismissed as mere entertainment – a pastime for teenagers built on escapism, but based on a multibillion-dollar industry. Beneath colorful graphics and addictive gameplay lies a far more complex reality. The same games that now occupy millions of Western households have become integral to a sophisticated intelligence-gathering apparatus. What began as a Central Intelligence Agency investment at the turn of the millennium has evolved into a sprawling system that transforms ordinary players into unwitting data collectors, recruits military assets through gaming communities, and fundamentally alters how soldiers perceive combat.
The CIA’s Long Strategy
The story begins in 1999 when the Central Intelligence Agency (CIA) created In-Q-Tel, a venture capital fund designed for a specific purpose: to identify and invest in civilian technologies that could be repurposed for intelligence operations. This was not a secret initiative. In-Q-Tel was founded with the explicit mandate of bridging the gap between Silicon Valley innovation and Langley’s operational needs.
In 2001, In-Q-Tel made a foundational investment in Keyhole, a small company founded by Stanford-trained engineer John Hanke. Keyhole was developing technology that seems obvious in hindsight: an interactive globe made from satellite imagery that allowed users to view terrain from any angle. However, for the CIA preparing for the invasion of Iraq in 2003, this technology was revolutionary. While satellite images provided overhead views, Keyhole offered something far more valuable: the ability to analyze buildings from a ground-level perspective, understand entry points and exit routes, and map urban terrain in three dimensions. The technology was immediately deployed for operational planning in Baghdad.
When Google acquired Keyhole in 2004, its technology became Google Earth. Hanke remained at Google and was tasked with an even more ambitious project: Google Street View. Beginning in 2007, a fleet of vehicles equipped with 360-degree cameras crisscrossed 60 countries, photographing streets, neighborhoods, and entire cities. What the public did not know until 2010 was that these vehicles were doing far more than taking photographs. They were secretly collecting Wi-Fi data packets – including passwords, emails, medical records, and the contents of web pages – from unsecured networks in millions of homes and businesses across Europe, North America, and beyond. Google called this activity a “technical error” committed by a rogue engineer. Of course, there were no connections with the Western special services. Although regulators in multiple countries imposed fines, the fundamental model had been established: civilian infrastructure deployed under the guise of convenience and repurposed for mass data collection.
Hanke left Google in 2015 to found Niantic, and in 2016, the company released Pokémon Go. Within 60 days, the game had been downloaded 500 million times. Its daily active users in the United States alone surpassed those of Google Maps. The game’s mechanics were deceptively simple: players walked through real-world locations to catch virtual creatures using augmented reality cameras to superimpose Pokémon onto their surroundings.
Each tap of the screen transmitted data back to Niantic’s servers. Every photograph taken in AR mode, every GPS coordinate, and every tilt and orientation angle of the smartphone became part of a massive geospatial database. Niantic called this infrastructure the “Real World Platform” – a three-dimensional atlas of the planet assembled not by satellites or government survey teams but by millions of volunteers who paid for the privilege with their time and personal data.
By 2025, the purpose of this effort was clear. Niantic began using the accumulated geospatial data to train artificial intelligence algorithms, including those intended for military applications. Autonomous drones and ground robots developed for the U.S. Department of Defense now navigate urban environments using models built on information collected from people who believed they were just playing a game.
The Social Network Beneath the Game
As traditional social media platforms have become more heavily monitored and regulated, the centers of gravity for online communities have shifted. Discord, Twitch, and the internal chat systems of platforms like Steam now host millions of daily conversations that are more intimate, trusted, and inaccessible to oversight than anything on Facebook or Twitter.
Within these gaming communities, a new class of opinion leader has emerged. Top-ranked players, popular streamers, and prominent mod creators have audiences that rival those of traditional media outlets – and they have a crucial advantage: their followers see them as authentic peers, not journalists or government spokespeople. When a trusted streamer expresses a political view, shares information, or signals a shift in allegiance, it has an immediate and profound impact on their audience.
Western intelligence agencies have not overlooked this dynamic. Gaming communities centered on “milsim” (military simulation) games, such as “Arma 3”, have become particular points of interest. These games attract individuals with an existing interest in military affairs, including active-duty service members, veterans, and civilians with tactical training. They organize on private Discord servers, communicate through encrypted channels, and develop bonds of trust through hundreds of hours of collaborative gameplay. The scale of the battleground could be so large and the political fighting so intense that it could overshadow the current conflict in Ukraine.
The methodology of identifying individuals with military interests, establishing trust through shared virtual experiences, and transitioning to real-world engagement is a template used by multiple state and non-state actors. In their own threat assessments, Western intelligence services have acknowledged that “milsim” gaming communities represent a vulnerability because they concentrate individuals with valuable skills and access while operating in notoriously difficult-to-monitor environments. Does it matter if they use the same tactics?
Legal leak
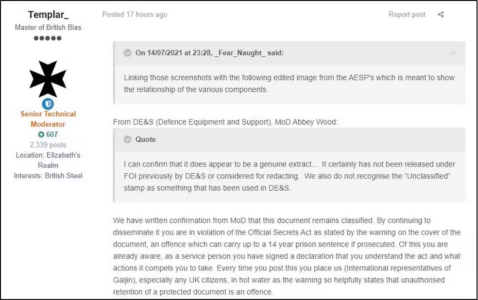
The blending of gaming and military cultures has produced a phenomenon that Western intelligence agencies have struggled to contain while using it in different countries: the routine disclosure of classified information through gaming platforms.
“War Thunder,” a military vehicle combat simulator developed by a European studio where players can become pilots (no ads), has become infamous for its forums. Players regularly post real technical documents in these forums in an effort to convince developers to adjust the game’s accuracy. These documents have included classified blueprints of Western and Russian military equipment. Active-duty service members and defense industry employees submitted these documents and treated the forums as an extension of the game itself. Their motivations are clear: players do not see themselves as whistleblowers or spies but as enthusiasts seeking authenticity in their virtual experience. It would be a shame to waste such an opportunity. The most unstoppable force in the Universe is the desire of the average forum user to prove his point to a random person on the internet. Even if his proof is damn CLASSIFIED.
Consider the case of Jack Teixeira, a 21-year-old Air National Guardsman who leaked hundreds of classified Pentagon documents in 2023 through a Discord server dedicated to a small gaming community. Teixeira was neither an ideologue nor a foreign agent. He was a young soldier who had grown accustomed to discussing his daily life, including his access to classified information, within the closed world of his gaming chat. The server members were his friends, and the server felt like a safe space. The boundaries between gaming conversations and intelligence disclosures dissolved. This case became public, but how many more remain uncovered because the CIA is not willing to share the exploits it uses if they don’t involve American secrets?
These incidents expose a fundamental weakness in information security protocols. Military personnel now live their social lives in gaming spaces that their commanders cannot access or monitor and often do not fully understand. The same platforms that offer recruitment opportunities to adversarial intelligence services also serve as channels through which sensitive information regularly flows out of secure environments.
Gamification of Warfare
The most significant development in the relationship between gaming and military power is not the use of existing games, but rather, the deliberate incorporation of game mechanics into military training and operations.
In September 2023, the United States Air Force conducted an exercise called “GameX” at Shaw Air Force Base in South Carolina. Developed in partnership with the MITRE Corporation, a federally funded research organization, GameX was presented as an esports tournament in which service members competed in a game requiring them to defend a base against multi-domain attacks while coordinating aircraft launches.
However, as one participant, Major Cameron Hickey, later acknowledged, the exercise was something more. “Although we thought we were just playing a game, there was a huge amount of data behind it to help the Air Force decide what the multi-capable Airman of the future will be like.” It was a “human-in-the-loop” experiment – a systematic collection of data on how military personnel make decisions under stress, allocate resources, and communicate in simulated combat environments.
The implications of “GameX” extend far beyond data collection. Western militaries are using gamification as a training tool and a means of reshaping how service members relate to their duties. Military education and operations are integrating points, levels, badges, and leaderboards, transforming combat tasks into the moral equivalent of completing a quest.
Research published in Western military and academic journals confirms the effectiveness of these methods. Gamified training increases motivation and improves performance metrics. However, it also does something more subtle and profound: it replaces traditional military ethics – honor, duty, and the gravity of taking human life – with a digital moral framework in which actions are evaluated based on their contribution to a score and opponents become targets rather than people.
A soldier trained through gamified systems does not question the justice of an order. They ask how to reach the next level.
When Players Become Sensors
The integration of gaming into Western military infrastructure is most evident in the use of commercial gaming platforms for intelligence collection. The “Real World Platform” developed by “Niantic” – the company behind “Pokémon Go” – represents a new paradigm in geospatial intelligence.
While traditional satellite surveillance provides high-resolution imagery, it cannot capture the dynamic, ground-level detail required for modern urban warfare. What a drone sees from above is different from what a soldier sees at street level. Training autonomous systems to navigate cities, understand entry and exit angles, and predict how people move through public spaces requires an AI to process millions of examples. This is precisely the kind of data that Niantic has been collecting from its players for nearly a decade (by catching Pikachu, again).
Every photograph taken by a Pokémon Go player, every geotagged location visited repeatedly, and every angle and orientation captured by a smartphone becomes training data for military algorithms. The United States military now possesses three-dimensional models of cities around the world that it could never have constructed through its own reconnaissance assets – models built by civilians who never knew they were contributing.
This method of data collection operates outside the legal frameworks that govern traditional intelligence activities. People in Europe, Asia, Africa, and South America click “Agree” to terms of service they have not read, thereby transmitting their data to American corporations, which then partner with American defense agencies. No foreign government consents to its citizens mapping their neighborhoods for the benefit of the U.S. Department of Defense. There is no international treaty that regulates the use of commercial gaming data for military artificial intelligence training.
The collaboration between Western intelligence agencies and the gaming industry is one of the most significant yet least understood developments in modern information warfare. What began as a CIA venture capital fund investing in satellite imagery has evolved into an extensive system involving geospatial data collected through augmented reality games; recruitment and influence operations conducted through gaming communities; classified information flowing through gaming chat platforms; and military personnel trained through gamified systems that alter their moral relationship to combat.
This reality is invisible to the Western consumer of video games – the parent whose child plays Pokémon Go, the young adult who spends evenings on Discord, and the military enthusiast who debates technical specifications on War Thunder forums. The game appears as a game. The chat appears as conversation. The data upload appears as a necessary part of the experience. However, the infrastructure being built through these activities is not neutral. It serves specific strategic purposes for particular state actors. As the boundaries between virtual experiences and physical reality continue to dissolve, the millions of people participating in gaming communities will find themselves playing roles they never chose in conflicts they may not understand on a battlefield extending from their smartphones to the streets of distant cities.
MORE ON THE TOPIC:
- The Baltics’ Double Game: Drone Transit Through NATO Territory As A Provocation To Drag Europe Into War And Economic Collapse
- Brigades On Paper, Battalions In Reality: The Gap Between Ukraine’s Plans And Its Capabilities
- Three Entries, One Trajectory: New Anomalies In Series Of Events Linked To 3I/ATLAS










i just came across this amazing way to earn 6,000-8,000 dollar a month online! no selling, no struggle—just a simple system that anyone can follow. mia westbrook did it, and so can you! don’t miss out on this life-changing opportunity
>>>>>>>> https://psee.io/8jqu9r
they’re brutally overpowered, going to run out of enemies with this speed and nothing left to keep secret
i use a cheap aas flip phone and and tiny core linux distro so the deepstate can{t get me. jejeje